Related Articles
- Uncharted Frequencies: The Surprising Role of Subcultures in Shaping Global Digital Landscapes
- Wired Whims: The Unexpected Role of Niche Online Communities in Shaping Global Digital Trends
- Fragmented Signals: Exploring the Shadows of Digital Divide in Emerging Economies and Its Impact on Global Unity
- Decoding the Invisible: How Microbial Communication Could Revolutionize Digital Interactions
- Cryptic Channels: How Encrypted Messaging Platforms Are Reshaping Trust and Transparency in Online Interactions
- Mysterious Modes: The Rise of Cryptographic Channels in Secret Online Dialogues and Their Hidden Impacts
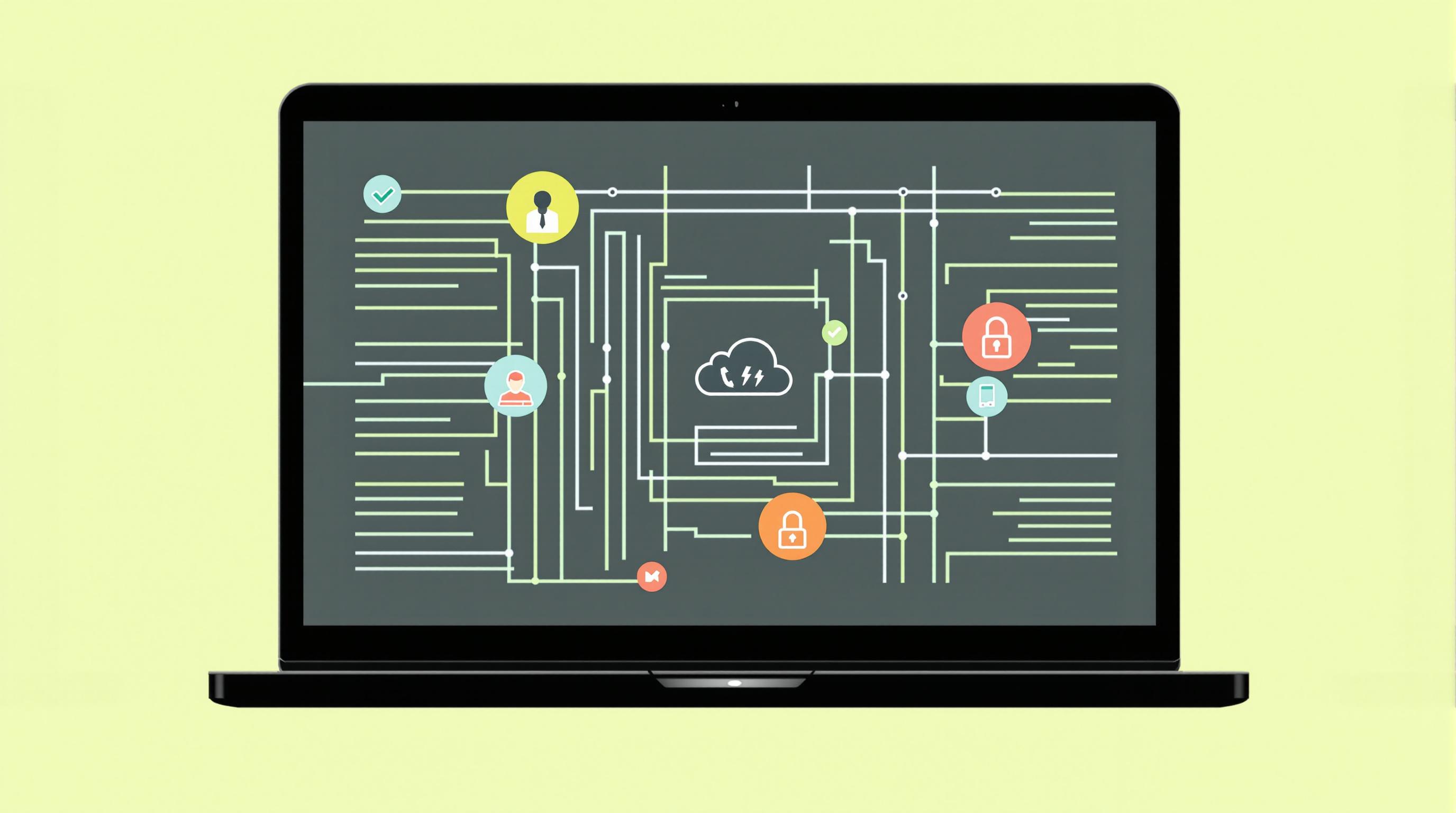
7 Intriguing Ways VoIP and Cloud Solutions Are Transforming Cybersecurity Resilience in a Hyperconnected World
7 Intriguing Ways VoIP and Cloud Solutions Are Transforming Cybersecurity Resilience in a Hyperconnected World
7 Intriguing Ways VoIP and Cloud Solutions Are Transforming Cybersecurity Resilience in a Hyperconnected World
1. Enhanced Communication Security
Voice over Internet Protocol (VoIP) and cloud solutions are redefining communication security by utilizing advanced encryption technologies. Unlike traditional phone systems, VoIP employs protocols such as Secure Real-time Transport Protocol (SRTP) and Transport Layer Security (TLS) to secure both voice data and signaling. This ensures that conversations remain confidential and are immune to eavesdropping attempts.
For businesses, the use of VoIP means not just improved communication but reinforced cybersecurity. A cloud-based VoIP platform can be regularly updated to incorporate the latest security measures, allowing organizations to adapt to evolving threats more swiftly. In contrast, older telephony systems often lack the necessary support for such robust security features.
Moreover, VoIP provides businesses with options like two-factor authentication, which adds an extra layer of security for access to communication platforms. By validating user identities through multiple methods, potential unauthorized access points are significantly reduced.
2. Real-Time Threat Detection
Cloud VoIP systems often integrate with advanced analytics and artificial intelligence (AI) tools to monitor network traffic and user behavior in real time. This continuous analysis enables organizations to detect suspicious activities almost immediately, giving them a head start in addressing potential breaches before they escalate.
Through machine learning, these systems can learn what constitutes normal behavior within the organization, making anomalies more apparent. For example, if a user's account is suddenly accessed from an unusual IP address, alerts can be triggered, and immediate actions can be taken to protect sensitive information.
This ability to leverage real-time data not only helps in identifying breaches but also streamlines incident response by providing crucial information promptly. As a result, organizations can investigate and mitigate threats swiftly, maintaining their cybersecurity integrity.
3. Decentralized Security Architecture
By moving communication systems to the cloud, businesses benefit from a decentralized security architecture. This twist in strategy reduces the risk that arises from centralized data points, which are typically prime targets for cybercriminals. Instead of concentrating sensitive data in one location, cloud solutions distribute this information across multiple servers.
The decentralized nature of cloud communication platforms adds redundancy to data storage, which is crucial for disaster recovery. In the event of a cyberattack or natural disaster, businesses can access their data from various locations, minimizing downtime and operational impacts. This resilience is essential in a hyperconnected world where maximum uptime is crucial.
Additionally, this distributed model allows for diverse security measures tailored to the unique requirements of different regions and jurisdictions. By employing location-specific compliance protocols, organizations can ensure they adhere to local regulations, further strengthening their cybersecurity posture.
4. Cost-Effective Security Solutions
Implementing cutting-edge cybersecurity measures through traditional means can be prohibitively expensive. However, VoIP and cloud services offer a more affordable alternative, allowing businesses to allocate their budgets more effectively. With reduced overhead for infrastructure and maintenance, organizations can invest in higher-quality cybersecurity tools.
Cloud providers often bundle security features into their services at no additional cost, further enhancing the value for businesses. Services such as regular software updates, automated backups, and security assessments allow companies to leverage advanced technologies without needing a large in-house IT staff.
Moreover, the pay-as-you-go pricing often associated with cloud services allows organizations to scale their security solutions as needed, accommodating growth without the burden of significant upfront expenditures. This flexibility ensures businesses can respond to new threats and adapt their security strategies dynamically.
5. Increased Collaboration and Awareness
VoIP and cloud solutions encourage a collaborative environment through shared platforms that enhance communication among team members and departments. This collaborative nature allows cybersecurity teams to communicate more effectively, share insights, and work together to identify potential vulnerabilities.
Moreover, the integration of VoIP within cloud services often includes collaboration tools that promote cybersecurity awareness among all users. Training can be implemented directly within the platform, ensuring that employees understand their roles in maintaining security and are informed of the latest threats.
This collective awareness fosters a culture of security, making it an intrinsic part of the work environment rather than an afterthought. When every employee is educated about cybersecurity best practices, organizations reduce the likelihood of human error leading to security breaches.
6. Adaptive Compliance Management
In a hyperconnected world, regulatory compliance is an ongoing challenge for businesses worldwide. Cloud-based VoIP systems are built with their compliance features in mind, automatically updating to reflect changes in legislation and industry standards. This adaptability simplifies the compliance process, allowing organizations to remain aligned with laws such as GDPR and HIPAA.
The incorporation of compliance monitoring tools directly into cloud platforms allows businesses to track their adherence to various regulations in real time. This feature ensures that any deviations can be corrected promptly, reducing the risk of penalties and fines that can arise from non-compliance.
Ultimately, organizations can focus on their core operations rather than spending excessive time on compliance checks. By leveraging these adaptive solutions, businesses increase their resilience against legal ramifications while maintaining robust cybersecurity practices.
7. Simplified Incident Response
VoIP and cloud solutions streamline incident response processes, enabling faster identification, containment, and resolution of cybersecurity incidents. Automated workflows can be established to react to specific threats, helping teams address issues swiftly and minimizing potential damage.
This quick response is made possible by the integration of various security tools, such as threat intelligence feeds, which inform businesses about emerging threats and vulnerabilities. By utilizing a consolidated dashboard where data from multiple sources is aggregated, organizations can gain a clearer picture of their cybersecurity landscape.
Additionally, post-incident analysis tools allow teams to assess the effectiveness of their response efforts. By learning from past incidents, organizations can refine and enhance their response strategies, creating a cycle of continuous improvement in their cybersecurity resilience.